With cyber threats making international news continually, we’ve all grown a bit weary and a bit tired of the topic but it doesn’t mean that the threat is going away, if anything it is getting worse. A Cyber Security Self Assessment may be the answer you are looking for to get a holistic idea of the current state of your …
Choosing a cloud provider
Many businesses are now looking towards “cloud computing” to provide them with the IT systems and services that they would have previously had in their office. Cloud computing encompasses many different technologies and services with a huge variety of “as a service” providers. This presents a considerable number of challenges for businesses over security, reliability, backup, performance and costs as …
Ransomware attacks – how to protect your business
The number of ransomware attacks is increasing at an alarming rate, making ransomware the biggest cyber threat that businesses are facing today. To see this disturbing trend, you only have to turn back the clock to the beginning of 2016. There was a 30 percent increase in the number of ransomware attacks in the first quarter of 2016 compared to …
Black Friday Cyber Crime
Black Friday cyber crime is probably the last thing you would think of when shopping online for unbelievable deals but it is a reality we must all face. Black Friday is a single day to take advantage of unbelievable discounts and limited stock. The day’s appeal is undeniable, but it’s also an opportune time for criminals to take advantage of …
Cyber Security – 10 ways you can educate your employees
Cyber Security and the internet of things has been the highlight of 2016 that has affected millions of people and tens of thousands of businesses. We’ve all heard about Cryptolocker, Heartbleed and now last week, BASH which have all received global media coverage. We’ve seen major retailers who have had customer details stolen and we’ve seen Ebay and other global on-line …
How to Test Your Backups
Regularly backing up your business’s files and computer systems is crucial, but it is just as important to test those backups at least once a year. You do not want to find out that your backup images or files are corrupt and thus useless when you are trying to recover from a natural disaster or cyberattack. But how do you …
Apple Provides Critical Update To Address Security Flaws in AirPort
The latest Apple Update for Security have been released by Apple for AirPort Base Station, their wi-fi enabled routers and devices. Affected models are AirPort Express, AirPort Extreme, and AirPort Time Capsule base stations with 802.11n and 802.11ac. In order to ensure the security of your personal information, I would recommend visiting the Apple security page for AirPort Base Station …
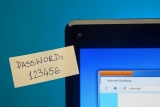
5 Ways Password Managers Can Help You Become More Organised and Efficient
Password managers are great for generating and storing strong passwords for online accounts. Many password managers, though, have additional features that let you easily store and access other types of information. Here are five ways you can take advantage of those features so that you can be more organised and efficient: 1. Auto-Fill Fields on Web Forms Many password managers …
Ransomware warning
Computer users are advised not to click on links or open attachments in uninvited or unexpected emails and be wary about the websites they visit as security researchers identify hazardous new versions of ransomware. They should keep regular backups of important files and store the backups in a location away from a network. Ransomware is a type of malware that …
The Top 5 Reasons Why Your Business Needs a Strong Firewall
In this age of global connectivity, protecting your business’s assets and data is more important than ever. Almost all businesses are connected to the Internet for a wide variety of services. These include email, search, social media, and cloud storage. While much of this traffic is outbound, the fact is that the same Internet connection also allows inbound traffic. That …
How to Avoid Creating Weak Passwords
You have likely heard that using strong passwords is an integral part of protecting a company’s data. But do you know what makes a password strong or weak? To find out, here is a quick weak passwords quiz: Take a look at the list of passwords below. (The quotes are not part of the passwords.) Which of the following are …
Insider Threats: How to Counter Internal Cybersecurity Risks
If you ask people about cybersecurity, they will probably start talking about hackers breaking into a company’s computers from hundreds of miles away. However, a threat just as destructive could be hiding inside that company’s offices. This is commonly referred to as insider threats. These insider threats typically fall into two groups. The first group consists of careless employees who …