If you are thinking about implementing Unified Communications Management in your business, it’s worth taking a deeper look into the many benefits. Here are my top 5 reasons why Unified Communications is a must in any business. 1. Incorporate different communication features to enhance collaboration What if you could multitask on different devices to get more done? With the the …
Ransomware attacks – how to protect your business
The number of ransomware attacks is increasing at an alarming rate, making ransomware the biggest cyber threat that businesses are facing today. To see this disturbing trend, you only have to turn back the clock to the beginning of 2016. There was a 30 percent increase in the number of ransomware attacks in the first quarter of 2016 compared to …
Cyber Security – 10 ways you can educate your employees
Cyber Security and the internet of things has been the highlight of 2016 that has affected millions of people and tens of thousands of businesses. We’ve all heard about Cryptolocker, Heartbleed and now last week, BASH which have all received global media coverage. We’ve seen major retailers who have had customer details stolen and we’ve seen Ebay and other global on-line …
8 Critical IT Supplier Questions you should ask
Dealing with IT suppliers and service providers is challenging for many businesses and many have concerns over reliability, security, cost as well as other factors. The key to hiring or dealing with a supplier is to do the research and leg work up front to ensure you know who you are dealing with, and the supplier you engage can service …
Apple Provides Critical Update To Address Security Flaws in AirPort
The latest Apple Update for Security have been released by Apple for AirPort Base Station, their wi-fi enabled routers and devices. Affected models are AirPort Express, AirPort Extreme, and AirPort Time Capsule base stations with 802.11n and 802.11ac. In order to ensure the security of your personal information, I would recommend visiting the Apple security page for AirPort Base Station …
4 IT Trends to Watch in 2016
What is going to happen to the IT world in 2016? While no one knows for sure, it is possible to make a few educated guesses based on current industry IT trends. The following predictions offer both early warnings and potential opportunities for business owners, helping them chart the best course forward. Here are four IT trends business owners should …
Ransomware warning
Computer users are advised not to click on links or open attachments in uninvited or unexpected emails and be wary about the websites they visit as security researchers identify hazardous new versions of ransomware. They should keep regular backups of important files and store the backups in a location away from a network. Ransomware is a type of malware that …
The Top 5 Reasons Why Your Business Needs a Strong Firewall
In this age of global connectivity, protecting your business’s assets and data is more important than ever. Almost all businesses are connected to the Internet for a wide variety of services. These include email, search, social media, and cloud storage. While much of this traffic is outbound, the fact is that the same Internet connection also allows inbound traffic. That …
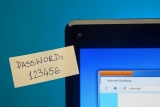
How to Avoid Creating Weak Passwords
You have likely heard that using strong passwords is an integral part of protecting a company’s data. But do you know what makes a password strong or weak? To find out, here is a quick weak passwords quiz: Take a look at the list of passwords below. (The quotes are not part of the passwords.) Which of the following are …
5 Ways That Automation Can Save You Time
Automation of routine tasks with applications is more efficient than using manual tools. Yet most companies rely on manual tools, according to a ServiceNow survey. Eighty percent of the 915 surveyed managers reported that their companies still use manual tools and that those tools cause significant delays. On average, the managers said they spend two days every week using them to …
Insider Threats: How to Counter Internal Cybersecurity Risks
If you ask people about cybersecurity, they will probably start talking about hackers breaking into a company’s computers from hundreds of miles away. However, a threat just as destructive could be hiding inside that company’s offices. This is commonly referred to as insider threats. These insider threats typically fall into two groups. The first group consists of careless employees who …
iTunes Scam Text Messages Spreading Malware
The latest iTunes Scam has been reported. Malicious individuals are reportedly sending scam text messages claiming to be from Apple’s music service iTunes to a large number of people. The message is believed to claim the recipient’s iTunes account has been frozen and asks them to click on a link to ‘validate their [iTunes] account’. However, people who click on …